“When in the Course of human events, it becomes necessary for one people to dissolve the digital bands which have connected them to another…”
By inviting foreign intelligence services to conduct espionage against American citizens, the Enclave has effectively “combined with others to subject us to a jurisdiction foreign to our constitution.”
The Declaration of Independence warns of a ruler who has “abdicated Government here, by declaring us out of his protection and waging war against us.” Today, that war isn’t fought with muskets; it’s fought with Content Detection Algorithms and the 14 Eyes Protocol.
I. The Mechanics of the “Noisy Cricket” Disclosure
The Chairman Cruz CISA Report provides the hard math for what we’ve called the “Censorship Laundry“. It reveals that CISA—an agency built to protect power grids—transformed itself into a “Thought Police“ force focused on policing American speech.
The Playbook:
- Switchboarding: CISA facilitated a process where they flagged American speech and “switched” it over to social media companies for removal.
- The Nonprofit Proxy: When the direct heat became too much, they “outsourced” the dirty work to third-party nonprofits like the Election Integrity Partnership (EIP).
- Actor-Agnostic Targeting: They deliberately ignored the distinction between “Foreign Threats” and “Domestic Speech,” effectively treating American citizens like enemy combatants.
II. The 14 Eyes: The Constitutional Back-Door
The truly terrifying reality is the 14 Eyes Protocol. The “Noisy Cricket” reveals that the NSA and its accomplices (GCHQ, BND, DGSE, etc.) have created a legal loophole: they cannot spy on their own citizens, but they can trade data with partners who do. * The 5 Eyes: The inner circle (US, UK, Canada, Australia, NZ) who share the deepest access to SIGINT.
- The 14 Eyes: The “SIGINT Seniors of Europe” who use the “lowest common privacy denominator” to ensure no digital activity goes uncaptured.
- The Back-Door Espionage: By “laundering” surveillance through foreign agencies, the government bypasses your 4th Amendment protections against unreasonable search and your 1st Amendment rights to free expression. They are “letting the enemy in” and paying them to monitor you.
III. The Maxwell Shield: Who Decides the Truth?
Why the massive effort at censorship? Because when you control the Memory Hole, you control the ledger of crimes.
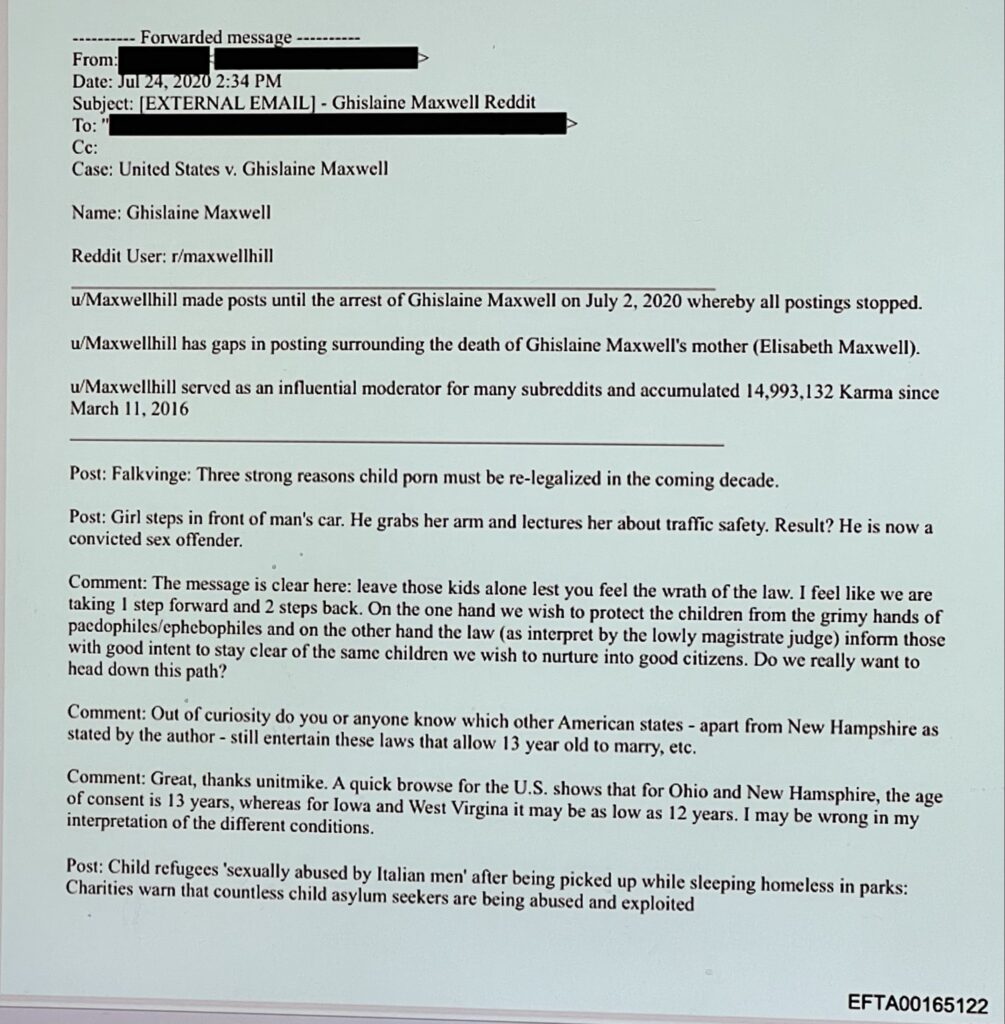
When people like Ghislaine Maxwell and the Global Elite control the “Content Moderation” parameters, they ensure the world remains blind to their operations.
- They label the “Dirt on the Dirtiest People” as “Misinformation” or “Malinformation” (factual information used “out of context”) to justify its incineration.
IV. The Death Blow: The Recoil of the Truth
The Founding Fathers were vehemently opposed to censorship because they knew that “He who has the power to silence you has the power to enslave you.” The CISA report confirms that these bureaucrats are now setting their sights on AI outputs, attempting to turn the next technological frontier into a permanent “Asphalt Cage” for the mind.
“They have forfeited our protection. We are reclaiming our Signal.”
SOVEREIGN ACTION REQUIRED:
- Check the 14 Eyes List: If your VPN or Email provider is based in a 14 Eyes country, your “encryption” is a prop.
- Submit to the Drop Box: If you have evidence of “Jawboning” (government pressure on platforms), submit your signal to the Deep State Drop Box.
- Stay Noisy: The recoil of the truth is the only thing the Council fears.
“Small Package. Big Boom. The Recoil is Liberty.”